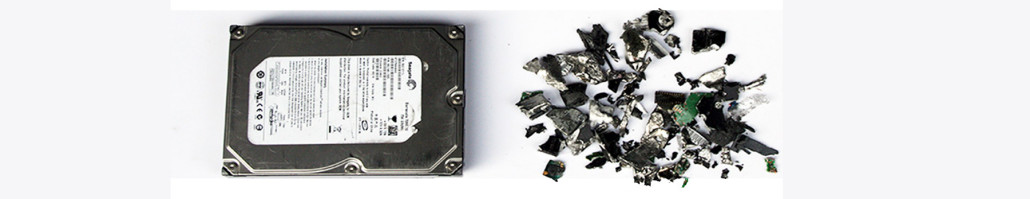
SHREDDING & DESTRUCTION – ON-SITE AND OFF-SITE SERVICES
Data Eliminate, part of the S2S Group, provides secure decommissioning, disposal and recycling services for Electrical and Electronic Equipment (EEE). The assets covered by these services include:
We can offer these services at the customer’s own premises using our mobile inventory cataloguing and destruction capability which enables all work to take place within your own security perimeter under the supervision of your own staff. Alternatively, we provide a fully auditable disposal and recycling process at our own secure facilities which incorporate detailed reporting on every item received, a method statement and the final outcome for each asset.
One-Off Jobs & Annual Contracts for Destruction & Disposal
One-Off Jobs and Annual Destruction Contracts are both available. Annual Service Contract Customers enjoy additional benefits such as secure containers for media storage prior to destruction and revenue share on any WEEE has a viable resale value after refurbishment.
All data destruction services are provided at three security grades which offer different sets of features. Our most popular service is our HMG / Corporate Grade. It is used by many HM Government Departments and approved the MOD. It is suitable for nearly all private sector and most public sector applications.